Privacy Access Control and Hacking Prevention of Blockchain Security.
Hello everyone I am @shahariar1 mod of Steem of Animals Community.I am From #Bangladesh
.png) |
|---|
How about we dig into the intriguing universe of Blockchain Security, zeroing in on Privacy, Access Control, and Hacking Prevention.
Blockchain and Security:
Blockchain technology has changed data security by addressing concerns connected with unapproved access and the rising danger of cyberattacks. This is the way it accomplishes this:
Decentralization: Blockchains work on a decentralized organization of hubs, making it provoking for a solitary element to control or control the framework. This decentralization improves security by decreasing the dependence on a focal power.
Immutability: Whenever information is recorded on a blockchain, it turns out to be essentially permanent. Altering authentic records is incredibly troublesome because of cryptographic hashing and agreement instruments.
Cryptography: Blockchain consolidates progressed cryptographic strategies to get information. Public key foundation (PKI) guarantees secure correspondence, computerized marks approve exchanges, and encryption safeguards delicate data.
 |
|---|
Security in Blockchain:
Security is significant in blockchain frameworks, particularly while managing delicate information. Here are some security improving perspectives:
Pseudonymity: Members in a blockchain network are distinguished by cryptographic addresses as opposed to genuine characters. This pseudonymity gives security while keeping up with straightforwardness.
Secret Transactions: Some blockchains (like Monero) utilize secret exchanges, where exchange sums are stowed away from general visibility. Just the shipper and collector approach this data.
Zero-Information Proofs: Zero-information verifications permit one party to demonstrate the legitimacy of an assertion without uncovering a particular subtleties. These are utilized to upgrade security in savvy contracts.
 |
|---|
Access Control in Blockchain:
Access control instruments guarantee that main approved gatherings can connect with the blockchain. This is the way blockchain handles access control:
Shrewd Contracts: Shrewd agreements characterize rules and authorizations for getting to explicit capabilities or information on the blockchain. They authorize access control in view of predefined conditions.
Job Based Admittance Control (RBAC): RBAC models can be executed inside brilliant agreements. Various jobs (e.g., administrator, client) have differing levels of admittance to explicit assets.
Blockchain Character Solutions: Projects such as Self-Sovereign Character (SSI) influence blockchain to make decentralized, client controlled personalities. Clients deal with their personality information and award access specifically.
 |
|---|
Hacking Counteraction:
Blockchain's innate plan gives vigorous security against different types of cyberattacks:
Agreement Mechanisms: Byzantine Adaptation to non-critical failure (BFT), Verification of Work (PoW), and Confirmation of Stake (PoS) keep vindictive entertainers from changing the blockchain's set of experiences.
Changeless Ledger: Whenever information is recorded, it can't be changed. This forestalls unapproved changes.
Tokenization: Tokenized resources (e.g., non-fungible tokens) upgrade security by addressing possession privileges on the blockchain.
 |
|---|
In rundown, blockchain's mix of decentralization, cryptography, and shrewd agreements adds to powerful security and protection. As we keep on investigating this interesting field, recollect that blockchain is definitely not a silver bulletit requires smart plan and continuous examination to address arising dangers.
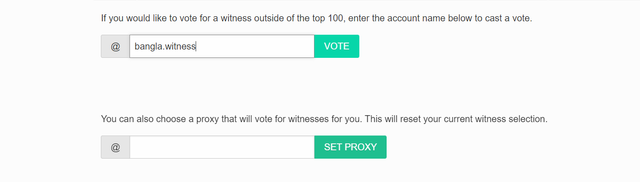
Support @bangla.Witness by Casting your witness vote
VOTE @bangla.witness as witness
X promote :
https://x.com/Shahari73599011/status/1777192988084752476
Note:- ✅
Regards,
@jueco